What is Azure Bastion?
Use Azure Bastion to securely connect to your Azure Virtual Machines.

We have probably all remoted into a desktop or a server at some point in our careers, it's something I've done a million times in order to carry out a task or check on something. The remote desktop (RDP) port, 3389, was something that was always available within on prem networks, you could connect into a server through RDP without an issue (most of the time) on an internal network. That option was very rarely, if ever open if you weren't sitting in the internal network. It's a way we are all familiar working within.
There are other ways of managing your servers, Windows Admin Centre being one way but sometimes you just need (or want) that RDP access to be open so how do you manage that when your servers are hosted in the Cloud? Do you open port 3389 up? Do you have a public IP address available? Both are options but not secure options as it does open you up to hackers and nefarious actors.
This is where Azure Bastion comes into play. 😀
What is Azure Bastion
Azure Bastion was announced in June 2019 and going fully Generally Available in November 2019 is a service within Azure that is designed to help provide that secure RDP (and SSH) access you need/want to your Azure based virtual machines. It's a fully managed Platform as a Service (PaaS) offering. The Bastion service allows you to securely connect to your virtual machines without having a public IP address assigned to it. You interact with the Bastion service through a browser session, the following browsers are supported, Microsoft Edge browser or Google Chrome on Windows. For Apple Mac, use Google Chrome browser. Microsoft Edge Chromium is also supported on both Windows and Mac.
Azure Bastion acts like that jump box many of us have probably had set up in our environment over the years. It isn't quite the same as those on prem jump boxes though, you don't get a server where you can store your files or install tools on to help. It just acts like a jump box. 😉 But that's one of the reasons I really like the service, it gives you the jump box functionality
You don't need to install software or an agent on the servers you want to access via the Bastion service, and it does not require an RDS CAL when used solely for administrative purposes.
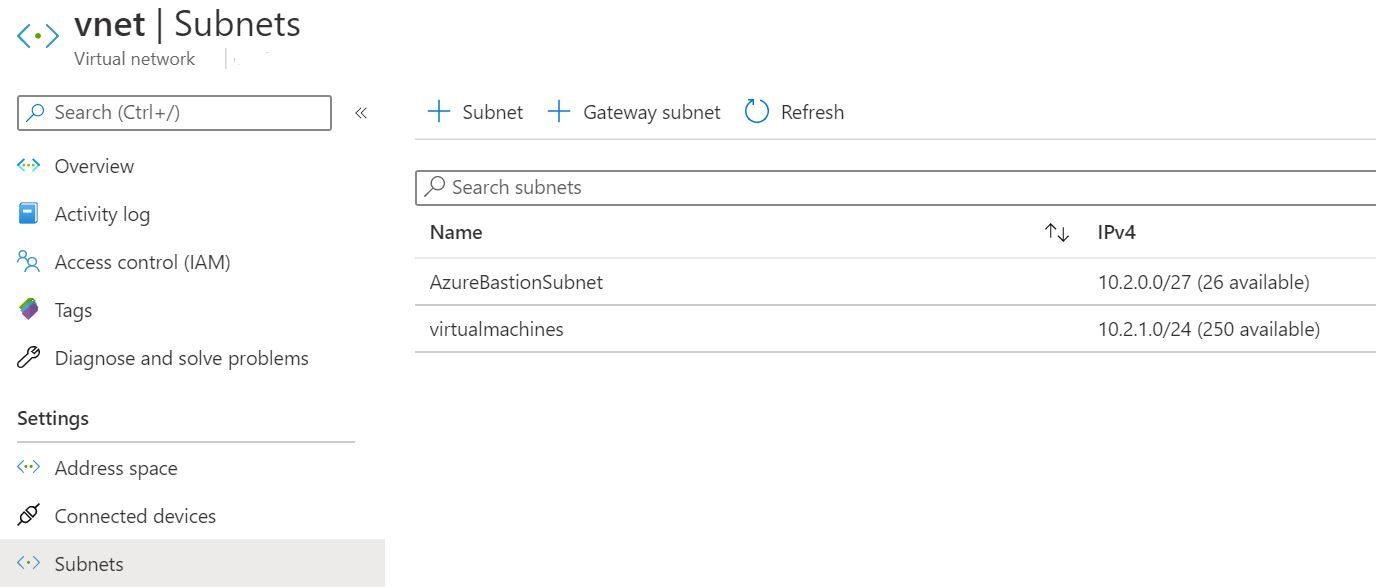
To deploy Azure Bastion successfully within your environment you need to deploy it to a subnet that is called AzureBastionSubnet with a CIDR of at least /27.
You can use Azure Bastion to connect to single virtual machines, virtual machines within scale sets, or virtual machines within DevTest Labs.
The service isn't available in all Azure regions, but you can check to see which ones it is available in here.
So if you are using virtual machines within Azure and looking for a secure method of connecting to them, consider Azure Bastion.